介绍:
CISSP MasterClass 是一个动态的、自定进度的认证计划,旨在适应您 。无论您是刚刚开始还是磨砺专业知识,该课程都会智能地关注您的知识差距,帮助您更聪明地学习,而不是更难学习。本课程由行业专家 Rob 和 John 开发,将深入的技术见解与战略学习工具相结合,指导您清晰而自信地掌握 CISSP

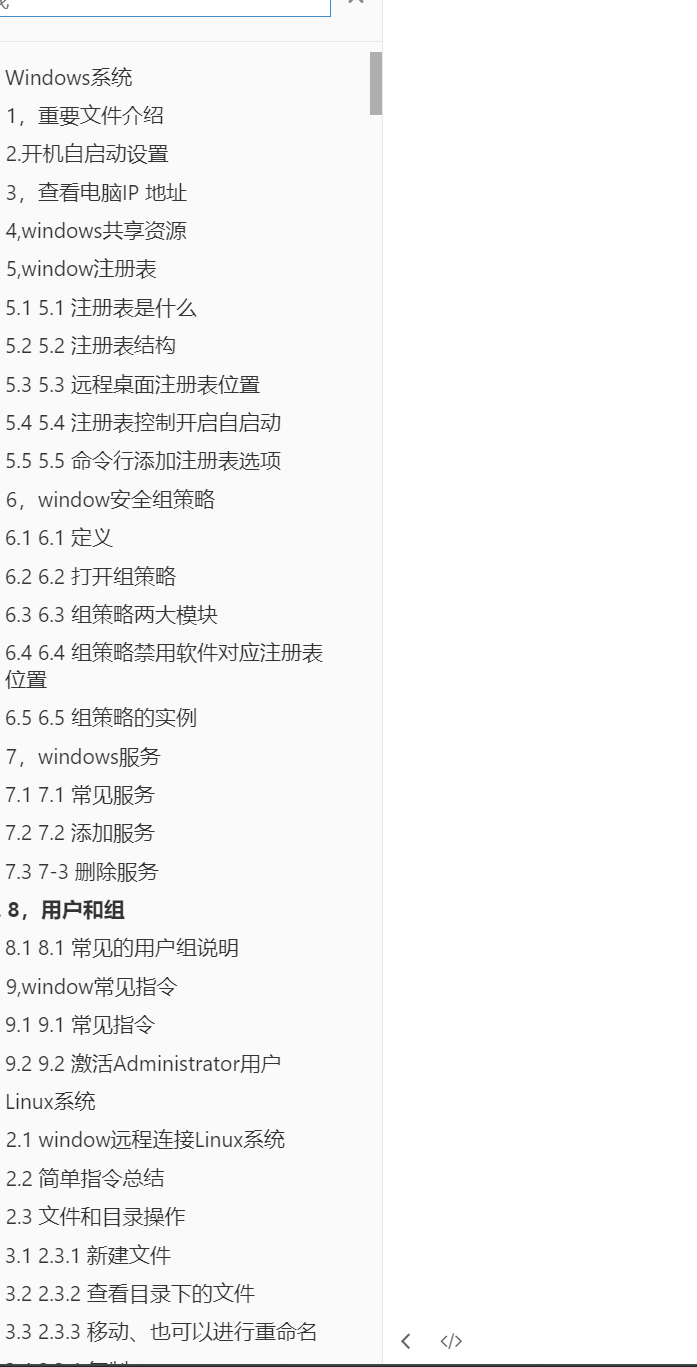
目录:
├── Domain 2 - Asset Security
│ ├── 2.3 Provision information and assets securely
│ │ ├── 02. Data Classification Policy bdziyi.com.mp4
│ │ ├── 01. Data Roles bdziyi.com.mp4
│ ├── 2.6 Determine data security controls and compliance requirements
│ │ ├── 02. Information obfuscation bdziyi.com.mp4
│ │ ├── 03. Scoping & Tailoring bdziyi.com.mp4
│ │ ├── 01. Protecting Data at Rest and in Transit .mp4
│ │ ├── 04. Data Protection Methods bdziyi.com.mp4
│ ├── 2.4 Manage data lifecycle
│ │ ├── 03. Data Remanence & Destruction Methods bdziyi.com.mp4
│ │ ├── 01. Data roles & lifecycle bdziyi.com.mp4
│ │ ├── 04. Object Reuse, SSD & Physical Destruction bdziyi.com.mp4
│ │ ├── 02. Manage the Data Life Cycle bdziyi.com.mp4
│ ├── 2.2 Establish information and asset handling requirements
│ │ ├── 01. Handling Requirements bdziyi.com.mp4
│ ├── 2.5 Ensure appropriate asset retention (e.g., End-of-Life (EOL), End-of-Support (EOS))
│ │ ├── 01. Data Archiving bdziyi.com.mp4
│ ├── 2.1 Identify and classify information and assets
│ │ ├── 02. Classification vs Categorization & Marking vs Labeling bdziyi.com.mp4
│ │ ├── 01. Introduction to Asset (Data) Classification bdziyi.com.mp4
├── Domain 3 - Security Architecture and Engineering
│ ├── 3.5 Assess and mitigate the vulnerabilities of security architectures, designs, and solution elements
│ │ ├── 15CROS~1_ev.mp4
│ │ ├── 03MORE~1_ev.mp4
│ │ ├── 08CHAR~1_ev.mp4
│ │ ├── 02VULN~1_ev.mp4
│ │ ├── 17. Input Validation_ev.mp4
│ │ ├── 16. SQL_Injection_bdziyi.com.mp4
│ │ ├── 12EDGE~1_ev.mp4
│ │ ├── 11COMP~1_ev.mp4
│ │ ├── 10CLOU~1_ev.mp4
│ │ ├── 01. Vulnerabilities_ev.mp4
│ │ ├── 04REDU~1_ev.mp4
│ │ ├── 09CLOU~1_ev.mp4
│ │ ├── 06INDU~1_ev.mp4
│ │ ├── 13. Sassy bdziyi.com.mp4
│ │ ├── 18CLIE~1_ev.mp4
│ │ ├── 05DIST~1_ev.mp4
│ │ ├── 14CROS~1_ev.mp4
│ │ ├── 07. OT vs ICS bdziyi.com.mp4
│ ├── 3.1 Research, implement and manage engineering processes using secure design principles
│ │ ├── 02. Cyber Kill Chain bdziyi.com.mp4
│ │ ├── 01. Secure design principles bdziyi.com.mp4
│ ├── 3.2 Understand the fundamental concepts of security models
│ │ ├── 05. Evaluation Criteria - Orange Book (TCSEC) & ITSEC. bdziyi.com.mp4
│ │ ├── 02. Enterprise Security Architectures bdziyi.com.mp4
│ │ ├── 03. Lattice Based Security Models - Bell-LaPadula & Biba bdziyi.com.mp4
│ │ ├── 06. Evaluation Criteria - Common Criteria bdziyi.com.mp4
│ │ ├── 04. Information Flow Models & Covert Channels bdziyi.com.mp4
│ │ ├── 01. Models & the Concept of Security bdziyi.com.mp4
│ ├── 3.8 Apply security principles to site and facility design
│ │ ├── 01. Intro to Physical Security bdziyi.com.mp4
│ ├── 3.9 Design site and facility security controls
│ │ ├── 01HOWD~1_ev.mp4
│ │ ├── 09. Ideal Temperature & Humidity Ranges bdziyi.com.mp4
│ │ ├── 07. Power - UPS & Generators and HVAC bdziyi.com.mp4
│ │ ├── 08. Power Degradation bdziyi.com.mp4
│ │ ├── 02. Physical Security Controls bdziyi.com.mp4
│ │ ├── 06. Skimming bdziyi.com.mp4
│ │ ├── 11. Fire Suppression bdziyi.com.mp4
│ │ ├── 05. Walls bdziyi.com.mp4
│ │ ├── 03. Locks bdziyi.com.mp4
│ │ ├── 04. Windows bdziyi.com.mp4
│ │ ├── 10. Fire Detection bdziyi.com.mp4
│ ├── 3.6 Select and determine cryptographic solutions
│ │ ├── 10. Hybrid Cryptography bdziyi.com.mp4
│ │ ├── 03. Cryptographic Definitions bdziyi.com.mp4
│ │ ├── 20. Cryptography Summary bdziyi.com.mp4
│ │ ├── 02. 5 Services of Cryptography bdziyi.com.mp4
│ │ ├── 14. Code Signing bdziyi.com.mp4
│ │ ├── 01. History of Cryptography bdziyi.com.mp4
│ │ ├── 15. Digital Certificates bdziyi.com.mp4
│ │ ├── 18. S_MIME bdziyi.com.mp4
│ │ ├── 11. Steganography & Null Ciphers bdziyi.com.mp4
│ │ ├── 05. Avoiding Patterns bdziyi.com.mp4
│ │ ├── 13. Digital Signatures bdziyi.com.mp4
│ │ ├── 16. Root of Trust bdziyi.com.mp4
│ │ ├── 17. Public Key Infastructure bdziyi.com.mp4
│ │ ├── 09. Diffie-Hellmann Key Exchange Protocol bdziyi.com.mp4
│ │ ├── 06. Stream vs. Block Ciphers bdziyi.com.mp4
│ │ ├── 07. Symmetric Cryptography bdziyi.com.mp4
│ │ ├── 08. Asymmetric Cryptography bdziyi.com.mp4
│ │ ├── 04. Substitution & Transposition bdziyi.com.mp4
│ │ ├── 12. Message Integrity Controls bdziyi.com.mp4
│ │ ├── 19. Key Management bdziyi.com.mp4
│ ├── 3.10 Manage the information system lifecycle
│ │ ├── 01. Information System Lifecycle bdziyi.com.mp4
│ ├── 3.4 Understand security capabilities of Information Systems
│ │ ├── 08. Abstraction, Virtualization & Hypervisors bdziyi.com.mp4
│ │ ├── 03. Example RMC, Security Kernel & TCB Question bdziyi.com.mp4
│ │ ├── 02. Details on RMC, Security Kernel, & TCB bdziyi.com.mp4
│ │ ├── 06. Firmware, System Kernel & Middleware bdziyi.com.mp4
│ │ ├── 05. Types of Storage bdziyi.com.mp4
│ │ ├── 09. More detail on VMs and Hypervisors bdziyi.com.mp4
│ │ ├── 04. Processors, States, Isolation & Memory Segmentation bdziyi.com.mp4
│ │ ├── 01. Overview of RMC, Security Kernel, & TCB bdziyi.com.mp4
│ │ ├── 07RING~1_ev.mp4
│ ├── 3.7 Understand methods of cryptanalytic attacks
│ │ ├── 03TERM~1_ev.mp4
│ │ ├── 01. Cryptanalysis - Cryptanalytic Attacks bdziyi.com.mp4
│ │ ├── 05. Birthday attack, Kerberos exploitation_ev.mp4
│ │ ├── 02CRYP~1_ev.mp4
│ │ ├── 04. Dictionary Attack, Rainbow Tables & Salting bdziyi.com.mp4
│ ├── 3.3 Select controls based upon systems security requirements
│ │ ├── 01. Security Control Frameworks bdziyi.com.mp4
├── Domain 6 - Security Assessment and Testing
│ ├── 6.4 Analyze test output and generate report
│ │ ├── 01. Test output bdziyi.com.mp4
│ ├── 6.2 Conduct security control testing
│ │ ├── 08VULN~1_ev.mp4
│ │ ├── 09. SCAP, Breach Attack Simulation & Compliance Checks bdziyi.com.mp4
│ │ ├── 06. Vulnerability Assessment & Penetration Testing bdziyi.com.mp4
│ │ ├── 02. Software Testing Techniques bdziyi.com.mp4
│ │ ├── 11. Operational & Regression Testing bdziyi.com.mp4
│ │ ├── 01. Software Testing Stages bdziyi.com.mp4
│ │ ├── 10. Log Review & Analysis bdziyi.com.mp4
│ │ ├── 03. Types of fuzzing bdziyi.com.mp4
│ │ ├── 05. Decision table & state-based analysis bdziyi.com.mp4
│ │ ├── 07. Red, Blue and Purple Teams bdziyi.com.mp4
│ │ ├── 04. Interactive Application Security Testing (IAST) bdziyi.com.mp4
│ ├── 6.1 Design and validate assessment, test, and audit strategies
│ │ ├── 01. Introduction to Security Assessment and Testing bdziyi.com.mp4
│ │ ├── 02. Location of Assessment bdziyi.com.mp4
│ ├── 6.5 Conduct or facilitate security audits
│ │ ├── 01. Third-Party Audit Reports bdziyi.com.mp4
│ ├── 6.3 Collect security process data (e.g., technical and administrative)
│ │ ├── 01. Metrics - KPIs & KRIs bdziyi.com.mp4
├── Mind Maps
│ ├── Domain 4 - Communication and Network Security
│ │ ├── 03. Network Defense bdziyi.com.mp4
│ │ ├── 04. Remote Access bdziyi.com.mp4
│ │ ├── 02. Networking bdziyi.com.mp4
│ │ ├── 01. Open Systems Interconnection (OSI) Model bdziyi.com.mp4
│ ├── Domain 6 - Security Assessment and Testing
│ │ ├── 01. Security Assessment and Testing bdziyi.com.mp4
│ │ ├── 03. Log Review & Analysis bdziyi.com.mp4
│ │ ├── 02. Identifying Vulnerabilities bdziyi.com.mp4
│ ├── Domain 7 - Security Operations
│ │ ├── 06. Business Continuity Management (BCM) bdziyi.com.mp4
│ │ ├── 03. Malware bdziyi.com.mp4
│ │ ├── 02. Incident Response bdziyi.com.mp4
│ │ ├── 05. Recovery Strategies bdziyi.com.mp4
│ │ ├── 01. Investigations bdziyi.com.mp4
│ │ ├── 04. Patching & Change Management bdziyi.com.mp4
│ ├── Domain 8 - Software Development Security
│ │ ├── 02. Databases bdziyi.com.mp4
│ │ ├── 01. Secure Software Development bdziyi.com.mp4
│ ├── Domain 1 - Security and Risk Management
│ │ ├── 01. Alignment of Security Function to Business Strategy bdziyi.com.mp4
│ │ ├── 02. Privacy & Intellectual Property bdziyi.com.mp4
│ │ ├── 03. Risk Management bdziyi.com.mp4
│ ├── Domain 2 - Asset Security
│ │ ├── 01. Asset Classification bdziyi.com.mp4
│ ├── Domain 3 - Security Architecture and Engineering
│ │ ├── 04. Vulnerabilities in Systems bdziyi.com.mp4
│ │ ├── 06. Cryptography bdziyi.com.mp4
│ │ ├── 01. Models, Secure Design Principles & Frameworks bdziyi.com.mp4
│ │ ├── 09. Physical Security bdziyi.com.mp4
│ │ ├── 02. Evaluation Criteria bdziyi.com.mp4
│ │ ├── 05. Cloud Computing bdziyi.com.mp4
│ │ ├── 07. Digital Signatures & Certificates, PKI & Key Management bdziyi.com.mp4
│ │ ├── 08. Cryptanalysis bdziyi.com.mp4
│ │ ├── 03. Trusted Computing Base (TCB) bdziyi.com.mp4
│ ├── Domain 5 - Identity and Access Management (IAM)
│ │ ├── 02. Single Sign-on - Federated Access bdziyi.com.mp4
│ │ ├── 01. Access Control bdziyi.com.mp4
├── Exam Strategy Practice Test
│ ├── Practice Question 20 bdziyi.com.mp4
│ ├── Practice Question 19 bdziyi.com.mp4
│ ├── Practice Question 5 bdziyi.com.mp4
│ ├── Practice Question 17 bdziyi.com.mp4
│ ├── Practice Question 6 bdziyi.com.mp4
│ ├── Practice Question 18 bdziyi.com.mp4
│ ├── Practice Question 8 bdziyi.com.mp4
│ ├── Exam Question Strategy bdziyi.com.mp4
│ ├── Practice Question 15 bdziyi.com.mp4
│ ├── Practice Question 4 bdziyi.com.mp4
│ ├── Practice Question 11 bdziyi.com.mp4
│ ├── DestCert+Printable+MindMaps.pdf
│ ├── Practice Question 12 bdziyi.com.mp4
│ ├── Practice Question 2 bdziyi.com.mp4
│ ├── Practice Question 21 bdziyi.com.mp4
│ ├── Practice Question 3 bdziyi.com.mp4
│ ├── Practice Question 13 bdziyi.com.mp4
│ ├── Practice Question 9 bdziyi.com.mp4
│ ├── Practice Question 1 bdziyi.com.mp4
│ ├── Practice Question 7 bdziyi.com.mp4
│ ├── Practice Question 14 bdziyi.com.mp4
│ ├── Practice Question 16 bdziyi.com.mp4
│ ├── CISSP+lists+and+processes+to+know.pdf
│ ├── Practice Question 10 bdziyi.com.mp4
├── Domain 4 - Communication and Network Security
│ ├── 4.3 Implement secure communication channels according to design
│ │ ├── 03. IPSec bdziyi.com.mp4
│ │ ├── 01. Tunnelling & VPN bdziyi.com.mp4
│ │ ├── 04. SSL_TLS & Remote Authentication bdziyi.com.mp4
│ │ ├── 02. GRE & split tunneling bdziyi.com.mp4
│ ├── 4.2 Secure network components
│ │ ├── 08. IDS & IPS - Detection Methods bdziyi.com.mp4
│ │ ├── 01. Network Defense Intro & Network Segmentation - Partitioning bdziyi.com.mp4
│ │ ├── 07. IDS & IPS - Analysis Engines bdziyi.com.mp4
│ │ ├── 03. Firewall Technologies bdziyi.com.mp4
│ │ ├── 06. IDS & IPS - Host & Network Based bdziyi.com.mp4
│ │ ├── 04. Firewall Architectures bdziyi.com.mp4
│ │ ├── 02. Proxy, NAT & PAT, and Private Addresses bdziyi.com.mp4
│ │ ├── 05. IDS & IPS bdziyi.com.mp4
│ ├── 4.1 Apply secure design principles in network architectures
│ │ ├── 16. IPv4 vs. IPv6 and Layer 3 Devices & Protocols bdziyi.com.mp4
│ │ ├── 12. Layer 2, Physical Addressing_ev.mp4
│ │ ├── 20. Common Ports bdziyi.com.mp4
│ │ ├── 17. Private IPv4 addresses & Network Classes (subnetting) bdziyi.com.mp4
│ │ ├── 01. Introduction to Networks & Protocols bdziyi.com.mp4
│ │ ├── 28. SDN architecture bdziyi.com.mp4
│ │ ├── 19. TCP 3-Way Handshake, Ports, and Layer 4 Protocols bdziyi.com.mp4
│ │ ├── 31. Monitoring and Management bdziyi.com.mp4
│ │ ├── 14. More detail on Authentication Protocols bdziyi.com.mp4
│ │ ├── 08. Dealing with Collisions bdziyi.com.mp4
│ │ ├── 10. Performance Metrics bdziyi.com.mp4
│ │ ├── 22. Convergence & VoIP bdziyi.com.mp4
│ │ ├── 15. Layer 3 & Logical Addressing bdziyi.com.mp4
│ │ ├── 03. Layer 1, Transmission Media & Crosstalk bdziyi.com.mp4
│ │ ├── 21. Layers 5, 6 & 7 bdziyi.com.mp4
│ │ ├── 11. Layer 1 Devices bdziyi.com.mp4
│ │ ├── 04. Transport Architecture bdziyi.com.mp4
│ │ ├── 23NETW~1_ev.mp4
│ │ ├── 06. Transmission Methods bdziyi.com.mp4
│ │ ├── 30. Wide Area Networks (WAN) bdziyi.com.mp4
│ │ ├── 02. The OSI Model bdziyi.com.mp4
│ │ ├── 29. Third-party connectivity bdziyi.com.mp4
│ │ ├── 18. Layer 4, TCP & UDP bdziyi.com.mp4
│ │ ├── 24. Network Attacks - DoS & DDoS, Spoofing & ARP Poisoning bdziyi.com.mp4
│ │ ├── 07. Traffic Flows bdziyi.com.mp4
│ │ ├── 25WIRE~1_ev.mp4
│ │ ├── 09. Physical Segmentation bdziyi.com.mp4
│ │ ├── 27. Network Virtualization Technologies - VLAN & SDN bdziyi.com.mp4
│ │ ├── 13. Authentication Protocols and Layer 2 Devices & Protocols bdziyi.com.mp4
│ │ ├── 26. Common tools bdziyi.com.mp4
│ │ ├── 05. Network Topologies bdziyi.com.mp4
│ ├── OSI-Model.pdf
├── Domain 1 - Security and Risk Management
│ ├── 1.5 Understand requirements for investigation types (i.e., administrative, criminal, civil, regulatory, industry standards)
│ │ ├── 01WEWI~1_ev.mp4
│ ├── 1.2 Understand and apply security concepts
│ │ ├── 01. Goals of Information Security bdziyi.com.mp4
│ │ ├── 02. 5 Pillars of Information Security bdziyi.com.mp4
│ ├── 1.12 Establish and maintain a security awareness, education, and training program
│ │ ├── 01. Awareness, Training & Education bdziyi.com.mp4
│ ├── 1.7 Identify, analyze, assess, prioritize, and implement Business Continuity (BC) requirements
│ │ ├── 01. We will cover BCM bdziyi.com.mp4
│ ├── 1.11 Apply Supply Chain Risk Management (SCRM) concepts
│ │ ├── 03. Risks Associated with the Acquisition of Products and Services bdziyi.com.mp4
│ │ ├── 01. Minimum Security Requirements & SLR bdziyi.com.mp4
│ │ ├── 02. SLA & Reporting bdziyi.com.mp4
│ ├── 1.4 Understand legal, regulatory, and compliance issues that pertain to information security in a holistic context
│ │ ├── 04PRIV~1_ev.mp4
│ │ ├── 02ITAR~1_ev.mp4
│ │ ├── 03. Privacy bdziyi.com.mp4
│ │ ├── 01INTE~1_ev.mp4
│ │ ├── 05ORGA~1_ev.mp4
│ ├── 1.3 Evaluate, apply, and sustain security governance principles
│ │ ├── 02. Security Roles & Responsibilities bdziyi.com.mp4
│ │ ├── 03. Due Care and Due Diligence bdziyi.com.mp4
│ │ ├── 01. Alignment of Security to the Business bdziyi.com.mp4
│ ├── 1.1 Understamd, adhere to, an promote professional ethics
│ │ ├── 01. Ethics bdziyi.com.mp4
│ ├── 1.6 Develop, document, and implement security policy, standards, procedures, and guidelines
│ │ ├── 01POLI~1_ev.mp4
│ ├── 1.9. Understand and apply risk management concepts
│ │ ├── 05. Risk Treatment bdziyi.com.mp4
│ │ ├── 02. Asset Valuation bdziyi.com.mp4
│ │ ├── 11. NIST 800-37 bdziyi.com.mp4
│ │ ├── 03. Risk Analysis bdziyi.com.mp4
│ │ ├── 06. Types of Controls bdziyi.com.mp4
│ │ ├── 10. Risk management Supply Chain & Risk Frameworks bdziyi.com.mp4
│ │ ├── 09. Selecting Controls bdziyi.com.mp4
│ │ ├── 01. Risk Management bdziyi.com.mp4
│ │ ├── 04. ALE Calculation bdziyi.com.mp4
│ │ ├── 07. Categorizing Controls bdziyi.com.mp4
│ │ ├── 08. Risk Management Terms Summary bdziyi.com.mp4
│ ├── 1.10 Understand and apply threat modeling concepts and methodologies
│ │ ├── 01. Threat Modeling Methodologies bdziyi.com.mp4
│ │ ├── 03. Social Engineering bdziyi.com.mp4
│ │ ├── 02. DREAD bdziyi.com.mp4
│ ├── 1.8 Contribute to and enforce personnel security policies and procedures
│ │ ├── 01. Personnel Security bdziyi.com.mp4
├── Domain 7 - Security Operations
│ ├── 7.1 Understand and comply with investigations
│ │ ├── 03. Digital Forensics & The Rules of Evidence bdziyi.com.mp4
│ │ ├── 01. Introduction to Security Operations & Forensic Investigation Process bdziyi.com.mp4
│ │ ├── 04. Types of Investigations bdziyi.com.mp4
│ │ ├── 02. Types of evidence bdziyi.com.mp4
│ ├── 7.7 Operate and maintain detection and preventative measures
│ │ ├── 03. Machine Learning and Artificial Intelligence based tools bdziyi.com.mp4
│ │ ├── 01. Malware bdziyi.com.mp4
│ │ ├── 02. Anti-malware bdziyi.com.mp4
│ ├── 7.2 Conduct logging and monitoring activities
│ │ ├── 01. Security Information and Event Management (SIEM) bdziyi.com.mp4
│ ├── 7.9 Understand and participate in change management processes
│ │ ├── 01. Change Management bdziyi.com.mp4
│ ├── 7.4 Apply foundational security operations concepts
│ │ ├── 01. Foundational Security Concepts bdziyi.com.mp4
│ ├── 7.15 Address personnel safety and security concerns
│ │ ├── 01. Personnel safety and security bdziyi.com.mp4
│ ├── 7.5 Apply resource protection
│ │ ├── 01. Protecting Media bdziyi.com.mp4
│ ├── 7.3 Perform Configuration Management (CM) (e.g., provisioning, baselining, automation)
│ │ ├── 01. Asset Inventory & Configuration Management bdziyi.com.mp4
│ ├── 7.8 Implement and support patch and vulnerability management
│ │ ├── 01. Patch Management bdziyi.com.mp4
│ ├── 7.11 Implement Disaster Recovery (DR) processes
│ │ ├── 03. The BIA Process bdziyi.com.mp4
│ │ ├── 01. BCM, BCP & DRP bdziyi.com.mp4
│ │ ├── 07. Declaring a Disaster bdziyi.com.mp4
│ │ ├── 08. Restoration Order bdziyi.com.mp4
│ │ ├── 04. RPO, RTO, WRT & MTD bdziyi.com.mp4
│ │ ├── 02. BCP-DRP Steps bdziyi.com.mp4
│ │ ├── 05. Zoom in on RPO & RTO bdziyi.com.mp4
│ │ ├── 06. External Dependencies bdziyi.com.mp4
│ ├── 7.6 Conduct incident management
│ │ ├── 01. Incident Response bdziyi.com.mp4
│ ├── 7.10 Implement recovery strategies
│ │ ├── 07. Recovery Site Strategies bdziyi.com.mp4
│ │ ├── 01. Failure modes bdziyi.com.mp4
│ │ ├── 02. Backup Storage Strategies bdziyi.com.mp4
│ │ ├── 03. Backup Storage Locations bdziyi.com.mp4
│ │ ├── 04. Spare Parts bdziyi.com.mp4
│ │ ├── 05. RAID bdziyi.com.mp4
│ │ ├── 06. Clustering & Redundancy bdziyi.com.mp4
│ ├── 7.13 Participate in Business Continuity (BC) planning and exercises
│ │ ├── 01. Goals of BCM bdziyi.com.mp4
│ ├── 7.14 Implement and manage physical security
│ │ ├── 01. We covered Physical Security in Domain 3 bdziyi.com.mp4
│ ├── 7.12 Test Disaster Recovery Plans (DRP)
│ │ ├── 01. Testing DR Plans bdziyi.com.mp4
├── Domain 5 - Identity and Access Management (IAM)
│ ├── 5.6 Implement authentication systems
│ │ ├── 01. Implement authentication systems bdziyi.com.mp4
│ ├── 5.1 Design identification and authentication strategy
│ │ ├── 01. Introduction to Access Control bdziyi.com.mp4
│ ├── 5.2 Authentication, Authorization and Accounting (AAA)
│ │ ├── 04. Password Vaults bdziyi.com.mp4
│ │ ├── 12. Federated Identity Management (FIM) & SAML bdziyi.com.mp4
│ │ ├── 05. Authentication Types (Factors) - Characteristics bdziyi.com.mp4
│ │ ├── 13. Just-in-Time (JIT) Access bdziyi.com.mp4
│ │ ├── 02. AAA bdziyi.com.mp4
│ │ ├── 10. Authenticator Assurance Levels (AAL) bdziyi.com.mp4
│ │ ├── 08. Password-less Authentication bdziyi.com.mp4
│ │ ├── 09. Single Sign-on, Kerberos & SESAME bdziyi.com.mp4
│ │ ├── 03. Authentication Types (Factors) - Knowledge & Ownership bdziyi.com.mp4
│ │ ├── 07. Single & Multi-Factor Authentication bdziyi.com.mp4
│ │ ├── 01. Access Control Services Overview bdziyi.com.mp4
│ │ ├── 06. Templates bdziyi.com.mp4
│ │ ├── 14. Principle of Access Control bdziyi.com.mp4
│ │ ├── 11. Session Management & Identity Proofing bdziyi.com.mp4
│ ├── 5.4 Implement and manage authorization mechanisms
│ │ ├── 04. Context - Attribute Based Access Controls bdziyi.com.mp4
│ │ ├── 01. Access Control Philosophies bdziyi.com.mp4
│ │ ├── 02. Types of RBAC bdziyi.com.mp4
│ │ ├── 06. Access Policy Enforcement bdziyi.com.mp4
│ │ ├── 03. Roles & Groups bdziyi.com.mp4
│ │ ├── 05. Access control summary bdziyi.com.mp4
│ ├── 5.5 Manage the identity and access provisioning lifecycle
│ │ ├── 02. Service Accounts bdziyi.com.mp4
│ │ ├── 01. Provisioning Lifecycle bdziyi.com.mp4
│ ├── 5.3 Federated identity with a third-party service
│ │ ├── 01. IDaaS bdziyi.com.mp4
├── Domain 8 - Software Development Security
│ ├── 8.3 Assess the effectiveness of software security
│ │ ├── 01. Software Assurance bdziyi.com.mp4
│ ├── 8.1 Understand and integrate security in the Software Development Life Cycle (SDLC)
│ │ ├── 02. Integrated Product Team (DevOps) bdziyi.com.mp4
│ │ ├── 05OPER~1_ev.mp4
│ │ ├── 01. SDLC vs. SLC Development Methodologies bdziyi.com.mp4
│ │ ├── 03. Canary testing & deployments bdziyi.com.mp4
│ │ ├── 04. Maturity Models bdziyi.com.mp4
│ ├── 8.2 Identify and apply security controls in software development ecosystems
│ │ ├── 01PROG~1_ev.mp4
│ │ ├── 03. Components of DBMS and Concurrency & Locks bdziyi.com.mp4
│ │ ├── 02. Secure Programming & obfuscation bdziyi.com.mp4
│ │ ├── 04. Metadata bdziyi.com.mp4
│ ├── 8.4 Assess security impact of acquired software
│ │ ├── 01. Acquiring Software bdziyi.com.mp4
│ │ ├── 02. Involve the Security Function is Assessing bdziyi.com.mp4
│ ├── 8.5 Define and apply secure coding guidelines and standards
│ │ ├── 01. Secure Coding, Buffer Overflows & APIs bdziyi.com.mp4
© 版权声明
文章版权归作者所有,未经允许请勿转载。
THE END










请登录后查看评论内容